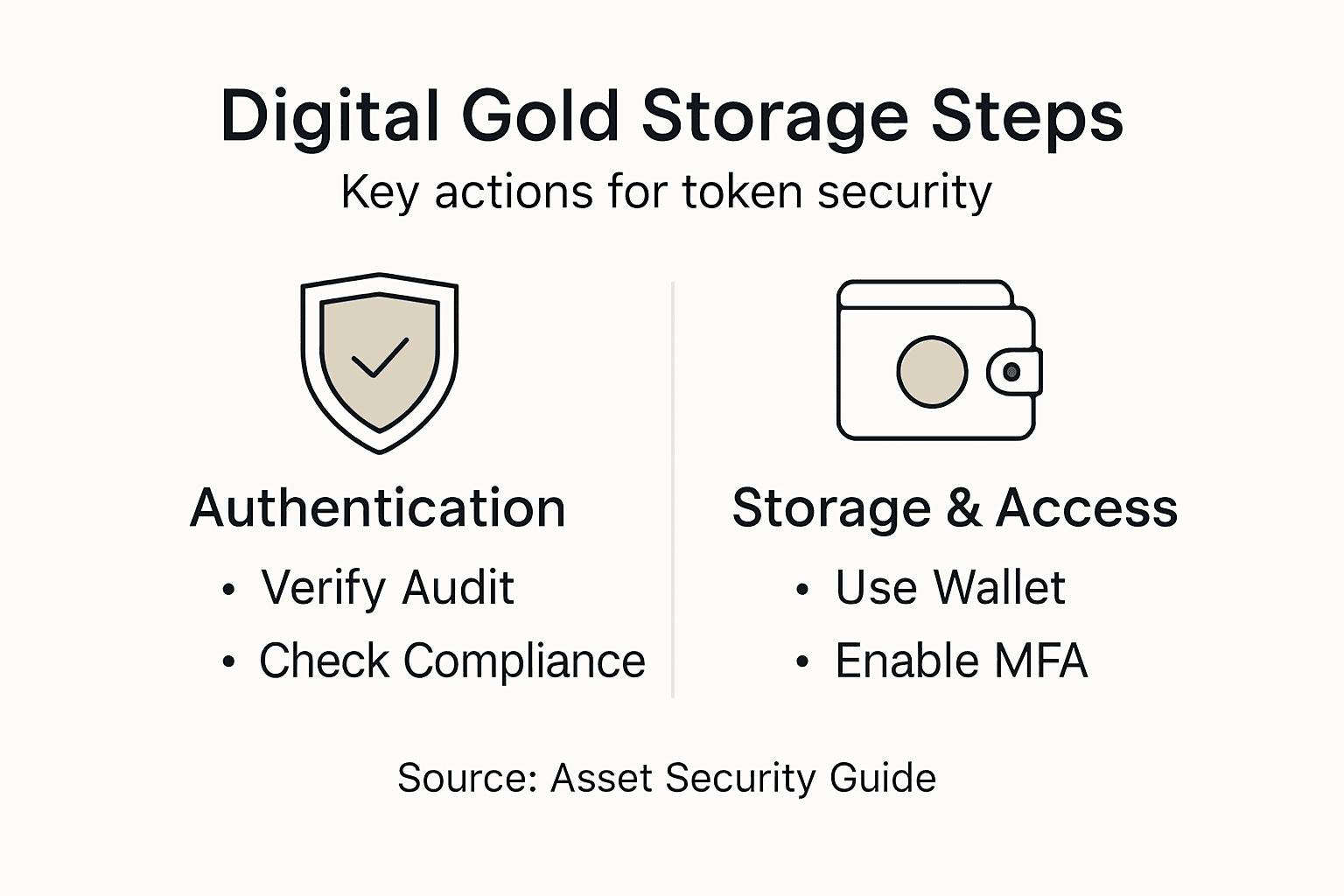
Secure Digital Gold Storage Guide for Asset-Backed Tokens

Protecting gold-backed digital assets starts with more than just trusting a token’s name. Security-conscious investors face complex decisions as regulations evolve, especially across European standards that govern asset-referenced tokens and digital storage compliance. This guide delivers actionable steps to validate token authenticity, choose compliant wallets, implement multi-factor authentication, and verify real asset reserves—ensuring your portfolio remains stable, transparent, and aligned with global regulatory expectations. Bold choices in secure storage start with thorough verification and reliable documentation.
Table of Contents
- Step 1: Assess Asset-Backed Token Authenticity
- Step 2: Select Compliant And Secure Storage Wallets
- Step 3: Implement Multi-Factor Authentication And Backups
- Step 4: Verify Digital Asset Reserves And Documentation
- Step 5: Monitor And Update Storage Practices Regularly
Quick Summary
| Key Insight | Explanation |
|---|---|
| 1. Verify Token Authenticity | Assess regulatory compliance and confirm asset details. Thorough documentation helps ensure a token’s legitimacy. |
| 2. Choose Secure Wallets | Select wallets with regulatory compliance and advanced security features. Prioritize options with multi-factor authentication. |
| 3. Implement Multi-Factor Authentication | Use layered security like biometrics and hardware tokens. This adds multiple barriers against unauthorized access. |
| 4. Regularly Monitor Reserves | Conduct audits and track documentation regularly. Stay updated with real-time asset monitoring to ensure transparency. |
| 5. Maintain Storage Best Practices | Schedule security audits, review access policies, and adapt to new technologies. Regular assessments improve overall security. |
Step 1: Assess asset-backed token authenticity
Validating the legitimacy of an asset-backed token requires a systematic approach that goes beyond surface-level promises. Understanding the critical evaluation steps can help investors protect their investments and identify tokens with genuine underlying value.
To assess an asset-backed token’s authenticity, start by examining its regulatory compliance through official EU token classification procedures. This involves investigating several key aspects:
- Regulatory Documentation: Request comprehensive documentation demonstrating legal compliance
- Asset Verification: Confirm precise details about the physical assets backing the token
- Third-Party Audits: Review independent financial audits and reserve reports
- Transparent Reserves: Validate the actual quantity and quality of underlying assets
Careful investors should conduct thorough due diligence by examining stablecoin regulatory frameworks that outline critical authentication requirements. This means analyzing not just marketing materials, but deep financial documentation that proves token legitimacy.
The authentication process requires checking multiple verification points – from regulatory status to actual asset backing percentage. Tokens with clear, verifiable connections to real-world assets provide significantly more security than abstract digital representations.
Pro tip: Request a complete asset reserve audit report before making any investment decisions and verify the documentation through multiple independent sources.
Step 2: Select compliant and secure storage wallets
Choosing the right storage wallet for your asset-backed tokens is a critical decision that directly impacts the security and accessibility of your digital investments. Your goal is to select a wallet that provides robust protection while maintaining regulatory compliance and ease of use.
When evaluating wallet options, focus on advanced digital asset wallet features that ensure comprehensive security. Consider these essential criteria:
- Regulatory Compliance: Verify the wallet meets current financial regulations
- Security Protocols: Assess multi-factor authentication capabilities
- Storage Type: Evaluate hot versus cold storage options
- Backup Mechanisms: Confirm robust key recovery and restoration processes
Institutional-grade wallets prioritize comprehensive security features that protect your digital assets against potential vulnerabilities.
Specifically, secure crypto wallet innovations now offer cutting-edge protections like biometric authentication, smart contract compatibility, and tamper-proof hardware designs. These advanced features significantly reduce the risk of unauthorized access and potential digital asset theft.

The selection process requires careful comparison of wallet capabilities, focusing on those that provide institutional-level security while maintaining user-friendly interfaces. Look for solutions that support multi-chain transactions and offer transparent key management processes.
Here’s how wallet storage methods compare for asset-backed tokens:
| Storage Method | Security Strength | Regulatory Alignment | Accessibility |
|---|---|---|---|
| Institutional Cold | Highest protection | Designed for compliance | Limited daily access |
| Consumer Hot | Moderate safeguards | May lack full adherence | Instant transactions |
| Hybrid Solutions | Layered security | Flexible for regulations | Custom access levels |
Pro tip: Always test a wallet’s security features with a small transaction before transferring substantial asset-backed token holdings.
Step 3: Implement multi-factor authentication and backups
Protecting your digital assets requires a comprehensive strategy that goes beyond basic password protection. By implementing robust multi-factor authentication and secure backup mechanisms, you can significantly reduce the risk of unauthorized access and potential asset loss.
Phishing-resistant authentication strategies are essential for safeguarding your digital tokens. Consider these critical authentication layers:
- Password Factor: Use a strong, unique password
- Biometric Authentication: Integrate fingerprint or facial recognition
- Physical Token: Employ hardware security keys
- Location Verification: Enable geographic access restrictions
Multi-factor authentication creates multiple barriers that significantly complicate unauthorized access attempts.
Effective multi-factor authentication implementation involves combining independent credentials that work synergistically. This approach means an attacker would need to compromise multiple authentication factors simultaneously, which is exponentially more difficult than breaching a single security measure.
Develop a comprehensive backup strategy that includes encrypted offline storage, distributed backup locations, and secure recovery mechanisms. Regularly test your backup and recovery processes to ensure they function correctly when you need them most.
Pro tip: Create encrypted backup copies of your authentication credentials in at least two geographically separated secure locations.
Step 4: Verify digital asset reserves and documentation
Validating the authenticity and backing of digital asset tokens requires a systematic and thorough verification process that goes beyond surface-level documentation. Your goal is to ensure complete transparency and confirm the actual physical reserves supporting your digital investments.
Decentralized reserve verification systems offer advanced techniques for authenticating asset reserves. Consider these critical verification steps:
- Documentation Review: Collect and scrutinize all reserve-related paperwork
- Third-Party Attestation: Request independent financial audits
- Real-Time Tracking: Utilize blockchain-based reserve monitoring tools
- Cross-Reference Verification: Compare official documentation with actual asset records
Comprehensive documentation verification creates a transparent framework that protects investor interests and prevents potential misrepresentations.
The comprehensive reporting framework established by financial regulatory bodies provides a structured approach to validating digital asset reserves. This involves examining detailed documentation that demonstrates the precise quantity, quality, and accessibility of underlying physical assets.
Effective verification requires a multifaceted approach that combines technological tools, independent audits, and meticulous document analysis. Look for tokens that provide real-time, transparent reporting of their asset reserves and maintain consistent, verifiable documentation.
Pro tip: Always request the most recent independent audit report and compare it against the current blockchain-recorded reserve data for complete verification.
Step 5: Monitor and update storage practices regularly
Maintaining the security and effectiveness of your digital asset storage requires consistent attention and proactive management. Your goal is to create a dynamic system that adapts to emerging technologies, regulatory changes, and potential security vulnerabilities.
Digital asset management best practices emphasize the importance of continuous monitoring and strategic updates. Consider implementing these critical maintenance strategies:
- Quarterly Security Audits: Conduct comprehensive reviews of storage infrastructure
- Access Control Updates: Regularly review and modify user permissions
- Technological Adaptation: Stay current with emerging security technologies
- Compliance Tracking: Monitor changing regulatory requirements
Regular monitoring transforms your storage strategy from static protection to a dynamic, responsive security ecosystem.
The global digital asset custody report highlights the critical nature of ongoing storage protocol reviews. This involves not just technical assessments, but a holistic approach that considers operational risks, technological innovations, and evolving security landscapes.
Effective monitoring requires establishing a structured review process that goes beyond occasional checkups. Create a systematic approach that includes regular technical assessments, security penetration testing, and comprehensive documentation updates to ensure your storage practices remain robust and adaptive.
Below is a quick summary of essential steps for monitoring digital asset storage:
| Maintenance Aspect | Purpose | Frequency |
|---|---|---|
| Security Audit | Detect vulnerabilities | Quarterly |
| Access Policy Review | Prevent unauthorized access | Every 3 months |
| Tech Update Assessment | Adopt new protections | Semi-annual |
| Compliance Status Check | Stay aligned with regulations | As laws are updated |
Pro tip: Schedule automated quarterly reviews and set up real-time alert systems that notify you of any potential security or compliance changes affecting your digital asset storage.
Secure Your Asset-Backed Digital Gold with Confidence
Investing in asset-backed tokens demands rigorous scrutiny of authenticity, transparent reserves, and secure storage solutions. This article clearly emphasizes the challenges of verifying regulatory compliance, multi-factor authentication, and ongoing storage monitoring to protect your digital gold. If you are seeking trustworthy tokens backed by real precious metals such as gold and silver, backed by detailed audits and live reserve disclosures, you need a partner that bridges traditional assets with blockchain technology.
Explore how Maya Preferred provides a secure, transparent platform for gold and silver-backed digital assets like MPRA, MPRD, and MCAT. We focus on clear documentation, independent audit reports, and compliance to give investors peace of mind when engaging with asset-backed cryptocurrencies. Visit Maya Preferred now to gain access to fully verified asset-backed tokens and elevate your investment with proven stability and transparent disclosures. Start securing your digital gold today by visiting Maya Preferred and learn more about our unique offerings and regulatory approach.
Frequently Asked Questions
How can I assess the authenticity of an asset-backed token?
To assess the authenticity of an asset-backed token, examine its regulatory compliance, review its regulatory documentation, and verify its asset backing through third-party audits. Start by requesting comprehensive documentation and validating the authenticity of its reserves to ensure a secure investment.
What features should I look for in a storage wallet for asset-backed tokens?
When selecting a storage wallet for asset-backed tokens, prioritize features such as regulatory compliance, robust security protocols, and backup mechanisms. Evaluate wallets that offer multi-factor authentication and secure cold storage options to protect your assets effectively.
How do I implement multi-factor authentication for my digital asset storage?
To implement multi-factor authentication, combine independent credentials like strong passwords, biometric authentication, and hardware security keys. Begin by setting up multiple authentication layers to significantly reduce the risk of unauthorized access to your digital assets.
What steps can I take to verify the documentation of digital asset reserves?
To verify the documentation of digital asset reserves, collect and scrutinize all relevant paperwork while requesting independent financial audits. Cross-reference official documentation with actual asset records to ensure transparency and validate the authenticity of your investments.
How often should I monitor and update my digital asset storage practices?
Monitor and update your digital asset storage practices at least quarterly by conducting security audits and reviewing access control policies. Implement a systematic approach to ensure your storage solutions remain secure and compliant with emerging regulations and technological changes.